In today’s information age, where almost every transaction is digitized, organizations face hundreds–and in some cases thousands–of vulnerabilities. The U.S. Department of Defense even kept a running list of all of its vulnerabilities. The hitch is that no one has the resources to close all of them across every application in a short period of time. That makes everyone anxious. It’s hard to sail a ship with confidence when you know it’s full of holes. You always wonder when and how the adversary will strike. Vulnerability management requires ruthless prioritization, and until now that’s been hard to do. How can the adversary use this vulnerability to strike? Which vulnerabilities are the most important? Defenders lacked a clear, comprehensive means of understanding how adversaries might exploit existing vulnerabilities to achieve their strategic objectives.
On the basis of new research from the Center for Threat-Informed Defense, you can now use the MITRE ATT&CK® framework and a threat-informed defense strategy to make smart vulnerability management decisions on the basis of known adversary behaviors. Defenders can now align vulnerability management and threat management, sharpening their cyberdefense capabilities on the basis of top-tier threats.
“Historically, vulnerability management and threat management have been separate disciplines,” says Jon Baker, Director of Research and Engineering at the Center, in a new blog post this week. “But in a risk-focused world, they need to be brought together.” AttackIQ worked closely with the Center to map vulnerabilities in the CVE® to the ATT&CK framework over the last year. The CVE Program, for those that don’t know it, aims to “identify, define, and catalog publicly disclosed cybersecurity vulnerabilities.” It categories vulnerabilities submitted by researchers over the world. The net result of this ATT&CK-CVE alignment is an improvement in organizational risk management.
How does it work?
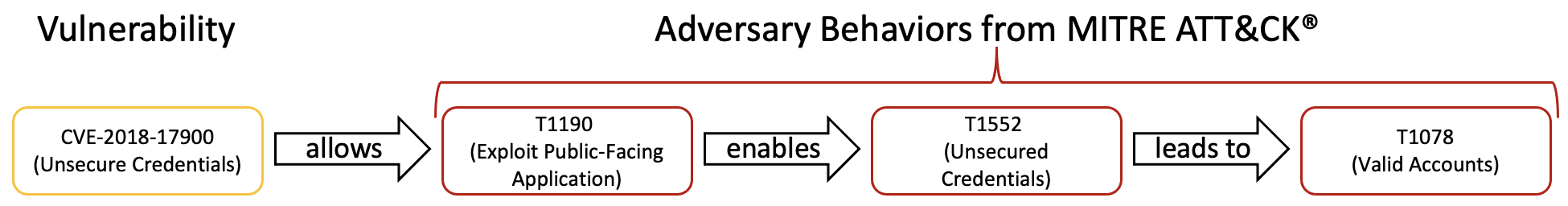
This research uses the MITRE ATT&CK framework to characterize the impact of each of the vulnerabilities described in the CVE list. Aligning CVE to ATT&CK provides a standard way to describe the methods adversaries use to exploit a vulnerability, and what adversaries may achieve by doing so. By using an ATT&CK technique to describe a vulnerability, defenders can more easily integrate vulnerabilities into their overall threat modeling and defense planning.
Let’s look at an example.
In this graphic, the attacker begins with the known vulnerability of “unsecure credentials” (CVE-2018-17900). This vulnerability allows the attacker to use the ATT&CK tactic Exploiting a Public Facing Website (Tactic 1190) which then enables the attacker to use the tactic of Unsecured Credentials (T1552). From there, they can move to Access Valid Accounts (T1078). This logical alignment, outlined in the Center’s research, shows how you can gain a strategic understanding of the adversary by aligning the two frameworks.
If you know which threat groups and tactics you are most concerned about, you can prioritize your vulnerability management. Close what you know needs to be closed first.
How does this approach help cyberdefenders strategically?
It optimizes an organization’s capabilities in threat modeling and risk management. With this information, defenders can use the ATT&CK-based impact information to inform their risk models. You can align your security control framework (i.e., NIST 800-53) to the threat behaviors in ATT&CK. Then use the CVEs and their ATT&CK technique references aligned to them to better understand how your compensating security controls will help you defend yourself against the vulnerability. Ultimately, this methodology creates a critical connection between vulnerability management and threat modeling, as the Center said in releasing its research on GitHub this week here.
This is important because it focuses organizations on the adversaries’ goals. Many vulnerability reports focus on the technical details of exploitation and its impact, but leave out the higher-level objectives and goals of the attacker. ATT&CK gives users the ability to see how an adversary might use the exploit to conduct an attack campaign. The application of this research will help defenders align their security controls against CVEs and ATT&CK techniques to optimize their cyberdefense operations and improve security effectiveness.
Next Steps for the Center’s Research
This exciting work is just beginning, and the Center is seeking collaborators from across the cybersecurity community. The following next steps are underway to adopt the methodology.
- CVE JSON Schema Enhancement: The Center has built a proposed CVE JSON schema extension to be integrated in the official CVE JSON Schema in November 2021. It introduces a taxonomy mapping object that can be used to include ATT&CK for describing impact. The CVE Program has approved this new schema change, and will come out with the final release of the new version.
- Integrate CVE Mappings: With the adoption of the proposed JSON schema changes, the Center aims to add its initial mappings to the official CVE List.
The next area of focus is community adoption. The Center and AttackIQ are seeking engagement with the CVE number authorities, threat intelligence teams, and end users. To make progress, defenders can review the methodology and engage the Center with any feedback. Vulnerability reporters are central to the adoption of this framework, and can further progress by including ATT&CK references to the vulnerability reports. Defenders can send inputs to [email protected] or file issues on the Center’s GitHub repository.
Enabling a Threat-Informed Defense
We at AttackIQ are focused on enabling a threat-informed defense and improving operational effectiveness for our customers and community. That is why we supported this research, as well as other meaningful programs as part of our collaboration with the Center for Threat-Informed Defense. Vulnerability management decisions need to be made on the basis of prioritized threats and adversary behaviors. After supporting this research over the last year, we will continue to produce content and develop our platform capabilities to help our customers align their vulnerability management strategies with the ATT&CK framework.