On July 2, 2021, the REvil ransomware group successfully exploited a zero-day vulnerability in the on-premise Kaseya VSA server, enabling a wide-scale supply chain cyber attack.
Kaseya, an American company, provides IT solutions and products to SMBs and MSPs. Kaseya VSA, the product targeted by REvil, provides endpoint management and network monitoring to thousands of customers. Despite the zero-day vulnerability being reported by the Dutch Institute for Vulnerability Disclosure (DIVD) CSIRT weeks before, and Kaseya working to release a patch, the timing of this attack falling over the U.S Independence Day weekend led to a perfect storm resulting in yet another supply chain attack. Sweden’s largest retailer Coop was one such example of a REvil victim having no option but to close almost 800 stores due to the impact. (For ongoing updates and notifications, please refer to the Kaseya incident page here).
Let’s dig in and see how the attack happened, how attack emulation could have helped, and what you can do to implement a threat-informed defense strategy to prepare yourself for similar threat actor behavior.
How the attack works
REvil managed to exploit the Kaseya VSA software, which in turn led to sending down a malicious payload to vulnerable VSA servers. Due to pre-configured antivirus exclusions for Kaseya VSA to function normally, the payload was allowed to be written to disk and then successfully deployed.
According to Sophos, the payload will first sleep for a random number of minutes before execution. It then executes a PowerShell command to disable native Microsoft security features such as Microsoft Defenders Realtime Protection. The certutil.exe living-off-the-land binary (LOLBin) is then used to decode the payload, a signed binary, which is used to drop an older vulnerable version of the Microsoft Antimalware Service executable. This enables the main ransomware DLL file to be sideloaded into memory using the legitimate and vulnerable Microsoft executable, and subsequently start the encryption process.
Detecting Kaseya VSA / REvil
Splunk, Cado Security, Sophos and many more security vendors have already released detection details and IOCs to assist with detecting and preventing this attack. Kaseya also released two PowerShell scripts on July 5, which can be run on VSA servers and any associated endpoints to help with identifying malicious files and intrusion attempts. Although the supply chain aspects of the attack are new, the underlying TTPs are in fact similar to previous REvil campaigns.
Let’s take a look at how you can emulate the Kaseya REvil intrusion with AttackIQ.
Validating your security controls for REvil
AttackIQ has released a first iteration of a new assessment template to emulate the behavior of Kaseya/REvil ransomware TTPs. The template is named “REvil ransomware Kaseya supply chain attack – July 2021” and can be found in the AttackIQ Platform within the Assessment Templates. The template includes coverage for the most recent attack chain observed in the Kaseya incident as part of the REvil ransomware supply chain attack. The assessment template includes 8 scenarios across 3 distinct tests, and requires zero configuration. If you wish to modify the existing scenario configuration, changing any configuration parameters is all possible and made simple through the platform.
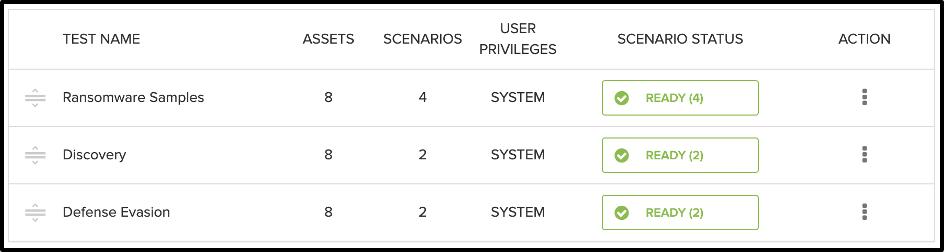
Contained within each test are the individual scenarios which are appropriately ordered to follow a similar attack sequence to that of Kaseya/REvil. The main focus of this assessment template is to test and validate your AV/NGAV, EDR/EPP, NGFS and content filtering controls. Depending on what security controls you have available in your environment, AttackIQ will automatically pre-populate the Compatible Technologies, highlighting which security controls you are able to test the REvil TTPs against. Each test and their corresponding scenarios are outlined below.
Note that for emulating additional REvil TTPs, AttackIQ has a separate template named “IcedID malware drops REvil ransomware.” This template includes coverage for the complete post-exploitation attack chain for the REvil ransomware family. The assessment template includes 18 scenarios across 6 tests as aligned to their corresponding MITRE ATT&CK tactic.
Ransomware samples
The ransomware samples test includes saving REvil ransomware samples to both the file system as well as to disk. This is the first test in identifying whether or not your security controls are working as expected.
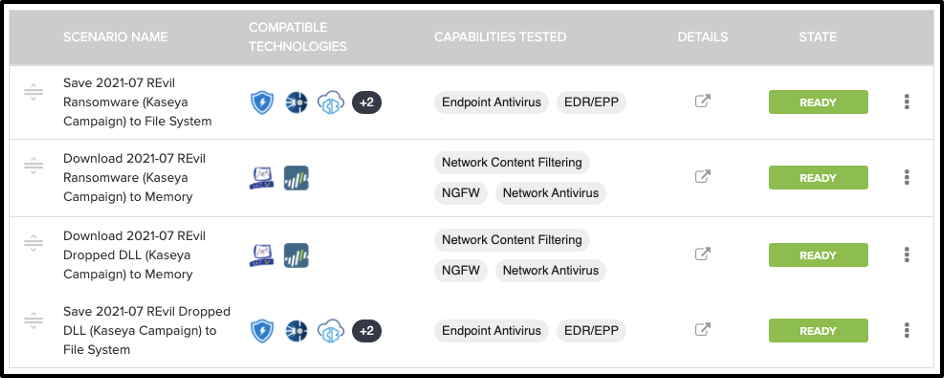
The “save to disk” scenarios enable you to test and validate your NGAV and EDR/EPP security tools. The “download to memory” uses the same two ransomware samples but is used for network testing of NGFW and content filtering security controls. From the two ransomware samples, one is a signed Windows executable used as the initial payload, and the other file is the malicious DLL executed by the older vulnerable version of the Microsoft Antimalware Service, which is responsible for the main encryption* routine.
Each ransomware sample is tested by saving it to disk and to memory. Saving the ransomware file to disk is a valuable test, as some AV/NGAV security tools may struggle with signature based detection, particularly if the binary is a signed executable or contains a custom encoding scheme. As many NGAV tools now use machine learning and behavioural based detection, this is a good way of putting such tools to the test.
*Note: This assessment template does not perform or emulate the encryption method used by REvil. If you wish to emulate this particular technique, refer to the scenario “Collect and Encrypt Files” from the Scenario Library which provides different encryption algorithms.
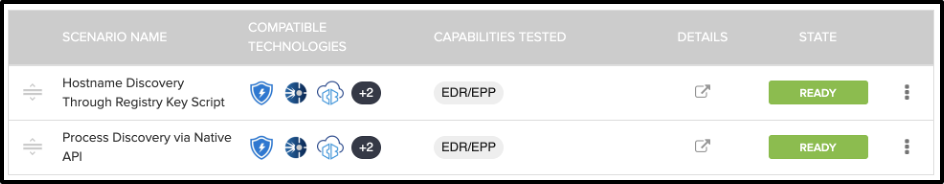
Discovery
The next test is for the discovery phase of the attack. The “hostname discovery through registry key script” scenario performs a hostname discovery by querying the Windows Registry. This is a common technique used by malware to obtain the local hostname of the victim host. The “Process Discovery via Native API” scenario uses Win32 API calls to query CreateToolhelp32Snapshot, Process32FirstW and Process32NextW. These API’s are common to malware due to the way in which malware often iterates through the running processes on a victim host, usually in order to evade certain security tools by killing any found processes. These same API’s were observed in the recent Kaseya REvil attack.
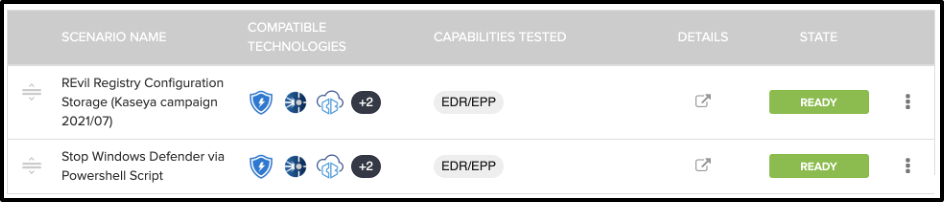
Defense evasion
The defense evasion test includes two scenarios:
- The “Registry Configuration Storage” scenario will attempt to write to the Windows Registry to the specific key “HKEY_CURRENT_USER\Software\BlackLivesMatter\”. This key has been commonly observed in multiple REvil campaigns, and is used to store public/private keys, C2 information, and other configuration information pertaining to the ransomware.
- The “Stop Windows Defender via Powershell script” scenario disables Windows Defender protections such as real time monitoring, behavior monitoring script scanning and other functions of Defender. This is particularly useful for an attacker to eliminate Windows Defender from the equation by disarming it, enabling the attacker a higher success rate for their final objective.
Reviewing the results
Once the assessment has been run, it’s time to review the results. From within the assessment results page, you can view individual results by overall prevention, overall detection, and a combined score. This enables you to obtain fast visibility as to which security controls performed well, and which ones require a closer inspection. Narrowing our scope further, we can also review the individual results at the scenario level. The example below shows us that the scenario that saved a REvil sample to the file system was both prevented and detected. Expanding out the detection with whichever integration we have configured, allows us to directly view the detection details from that given security control.
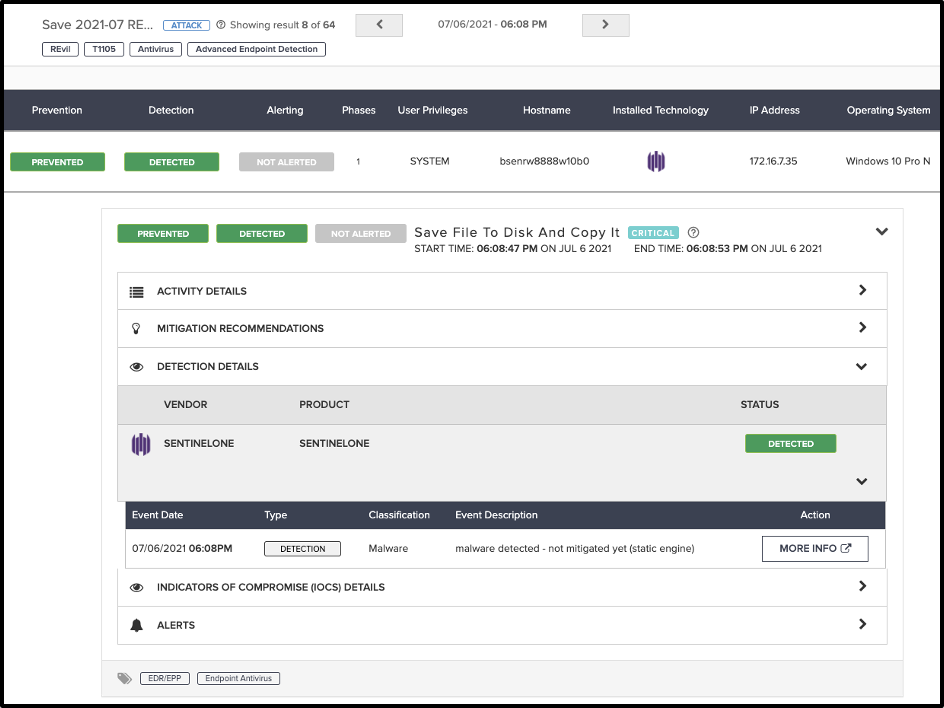
Other areas of interest are the activity details, which list the scenario activity. This is useful in helping to identify how far the scenario was able to execute its TTPs. The mitigation recommendations are useful to begin discussions around what mitigation actions are required, if at all.
It’s clear: Now is the time for proactive, threat-informed defense
Keeping ahead of attackers and understanding how they operate—so you can properly defend— is becoming more and more critical in light of this attack and many more in recent events that preceded it.
Now that you and your security teams are equipped with all of these insights, it’s time to start collaborating and working together towards a threat-informed defense. Increased knowledge and visibility into how your security controls prevent and/or detect is the first step, but understanding and developing processes, as well as developing skills for the people driving these tools, greatly benefits the overall security posture of your organization.
Here’s how you can get started:
- Learn more about how to stand up and enact a threat-informed defense strategy in the Threat-Informed Defense 101 guide
- Get free cybersecurity training online for you and your team with AttackIQ Academy, featuring courses on Foundations of MITRE ATT&CK, Breach and Attack Simulation, Purple Teaming, and more. Register now
- See security optimization in action in one of our weekly demos featuring topics around operationalizing MITRE ATT&CK, purple teaming, automated testing, and more.






