Recently, AttackIQ was notified that an Iranian threat actor had created a fake domain and fraudulent website (attackiq[.]ir) impersonating AttackIQ and abusing the company brand. This blog is an account of what happened and how AttackIQ responded, and it aims to provide insights to help organizations prepare to deal with similar Brand Reputation Abuse situations. This type of brand reputation impersonation happens with increasing frequency [1] to organizations across the globe, and our goal is to be transparent about what happened and help other organizations that may find themselves in a similar situation.
What Happened
On October 15, 2021, AttackIQ was notified that a group operating on network infrastructure hosted in Iran (attackiq[.]ir) was attempting to impersonate the AttackIQ brand. AttackIQ analyzed the situation and is taking steps to address the issue. High level points:
- This was strictly brand reputational impersonation and did not involve any AttackIQ owned and operated infrastructure.
- The group registered a top-level domain using AttackIQ in the domain name (attackiq[.]ir). Such a bad faith registration is known as “cybersquatting.”
- AttackIQ has filed a UDRP claim to document brand impersonation abuse with ICANN.
- AttackIQ has contacted key partners to facilitate a takedown of the abusive domain.
- We recommend that users do not attempt to visit the fake domain and website as it may contain malware.
What is Top Level Domain Squatting (a.k.a. “cybersquatting”) and Brand Impersonation
Top-level domain squatting generally has the intention of causing reputational damage to a particular brand. Domain squatting usually involves phishing campaigns to acquire customer data or to spread abusive advertisements about a brand.
This technique has been used for decades and continues to be pervasive today. In fact, MITRE ATT&CK has published a sub-technique, referred to as “Acquire Infrastructure: Domains” so our community can have a common language when referring to such an attack technique [2].
There are innumerable examples of this technique being used. In 2019, Microsoft took down 99 domains operated by Iranian state threat actors [3]. In that particular operation, Iranian threat actors known in cybersecurity circles as APT35, Phosphorus, Charming Kitten, and the Ajax Security Team [4] used the registered domains incorporating brand names (including Microsoft and Yahoo) in spear-phishing campaigns to trick unsuspecting users to provide their credentials.
Take-downs of such domains can be difficult depending on the regions in which the domain is registered, but in this operation Microsoft used legal action to take down the registered domains.
Illegitimate registered domain names are only part of the reputational abuse though. The other tactics of the abuse relate to how threat actors are able to scrape a brand’s content and copy it to a fake website in order to resemble the brand and trick the user to provide sensitive information such as credentials, or other confidential and sensitive information.
Although more sophisticated threat actors will build each component from scratch when targeting a brand, it is more common in less sophisticated cases for them to use toolkits like the social engineering toolkit (SET) [5] [6]. SET is a free and open source tool available in Kali Linux, or it can be downloaded directly and installed from Github. This particular toolkit helps a brand abuser to generate a standard metasploit executable and allow the group to set the command and control (C2) domain. SET and similar toolkits will typically help clone related content from the legitimate website to a phishing version of the website in order to trick a user into thinking they are interacting with the real brand.
In the case of AttackIQ’s research into our brand impersonation, we found evidence that the attacker most likely used SET and that all of the components were crafted with generic and unsophisticated toolkits and methods.
Technical Details
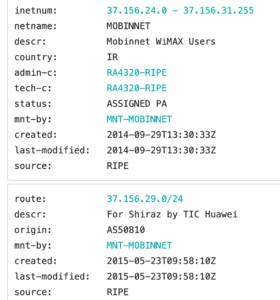
The original malware was identified through open source threat intelligence and sandboxing telemetry. Researchers monitoring these resources noticed malware using a derivative of the AttackIQ name. At the same time, the threat intelligence community observed a new top level domain register attackiq[.]ir on October 4, 2021, subsequently publishing the fake website and mimicking the AttackIQ and MITRE ATT&CK® websites.
Vendors identified and analyzed the binary, and recognized it as malicious. It is designed to initiate C2 calls to the attackiq[.]ir domain. The resolving IP of 37.156.29.168 hosts other websites as well, indicating it is a hosted infrastructure. The payload itself has been identified as a Metasploit binary payload intended at a minimum to establish a C2 communication and a foothold, but the intention is unknown.
Although we have seen no evidence of such actions, users should be aware that threat actors in this region typically operate in a similar fashion, leveraging recognized brands through phishing campaigns to establish an initial foothold on a network. We, therefore, urge customers and the public to remain especially vigilant of potential phishing efforts that could impersonate our domain
Indicators of Compromise
attackiq[.]ir
37[.]156[.]29[.]168
Hashes (SHA-256)
09aacaa52a33c386bda3b824a813211b82cde2ea7c8af4f44abb42cce5e80631
De2c2d99457e987fde9a2514b451d84c50f18eca04d77fbc1471894e0586ca73
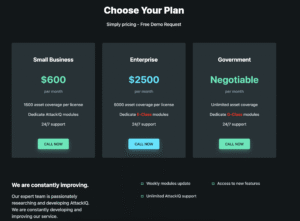
Screenshots of attackiq[.]ir


How We Responded
As soon as we became aware of the existence of a fake domain and website impersonating AttackIQ, we took the following steps to remediate the issue:
- Filed a UDRP claim to document illegal brand impersonation abuse with the World Intellectual Property Organization (WIPO);
- contacted key partners to assist in a take-down request; and
- communicated to the public about our findings.
How to Protect Yourself from Brand Impersonation
Block attacks
Organizations should block email phishing attacks that use domain squatting. To do so, users should implement email gateways and spam controls that can use various technologies to analyze normal versus anomalous behavior. They should also analyze malicious and suspicious links and attachments before they get to a user. These actions will help minimize click throughs of any attempted phishing emails. There are a range of mature anti-phishing software providers available on the open market.
Set up DMARC reporting and enforcement
You can get visibility into domain fraud using DMARC authentication to protect against domain spoofing and brand hijacking. DMARC reporting provides visibility into how your email domain is used, which in turn allows you to set up DMARC enforcement policies that will prevent spoofing of your domain.
Register similar names
Consider buying domains with multiple extensions, such as .com, .co, .biz, etc., to prevent cybersquatters from buying them and abusing your brand. Research common misspellings of your domain and consider registering them as well.
Sign-up and register for digital risk and brand protection
There are numerous services available to register your brand, trademark, and domains to be notified when brand reputation is at risk and minimize brand damage and in addition more easily request a take-down effort be mobilized against an abusing domain.
Contact the domain owner or file a UDRP claim or court proceeding
Note: UDRP, led by WIPO, was introduced as a tool to help brand owners tackle cybersquatting
If you believe a domain name infringes on your copyright or trademark, contact the owner of the domain or file a UDRP claim or court proceeding.
You will need to file a complaint, being careful to communicate it in as many ways as possible. Choose an Internet Corporation for Assigned Names and Numbers (ICANN)-approved provider to oversee administrative proceedings, and be prepared to show evidence of trademark or copyright ownership on your part and bad faith on the part of the accused domain squatter.[7]
Complete information is available on ICANN’s website.
Conclusion
Adversaries will continue to use sophisticated social engineering techniques to facilitate their nefarious goals. Brand Reputation Impersonation is just one of the many techniques for which organizations need to prepare. At AttackIQ, we are dedicated to transparency and constant education for the cybersecurity community, and you can find additional educational material at academy.attackiq.com. Please feel free to reach out to us at [email protected] with any additional questions.






