Author: Jonathan Reiber
February 14, 2023
AttackIQ is democratiziing the practice of threat-informed defense and adversary emulation, including by funding research from the Center for Threat-Informed Defense on micro-emulation planning. Learn more out how we put adversary emulation into practice in the AttackIQ Security Optimization Platform.
December 13, 2022
OpenAI’s ChatGPT can tell you exactly how to use BAS to improve your cyberdefense effectiveness. But it won’t help you with the Russian military specifically, and that’s a very good thing. See below for why OpenAI deserves credit for this algorithmic limit.
December 12, 2022
We asked OpenAI’s ChaptGPT to write a 750-800 word blog post about breach and attack simulation (BAS) in the voice of Langston Hughes. It did great; see below. And well-done, team OpenAI.
October 31, 2022
One of Ash Carter’s former speechwriters and special assistants reflects on the lessons the Secretary of Defense leaves behind.
March 11, 2022
AttackIQ and the Center for Threat-Informed Defense are furthering the art of adversary emulation with the Center’s new Attack Flow project. Building on our deep research partnership with the Center, AttackIQ’s Attack Graphs emulate the adversary with specificity and realism to test advanced cyberdefense technologies against multi-stage attacks. Read on for more.
January 19, 2022
Ransomware is a vexing challenge and attacks have doubled since 2020, but there is a path out of the problem. In this new guide, Countering Ransomware with MITRE ATT&CK, AttackIQ outlines clear, practical steps to test and validate that your security program performs against ransomware. The trick is to prepare, and the path to follow is a threat-informed defense. Check it out and come join us for a technical demonstration of our ransomware capabilities on January 27.
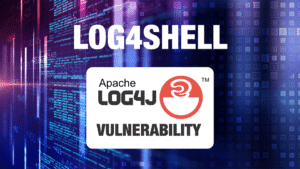
December 13, 2021
This article focuses on helping organizations to assess the effectiveness of their compensating controls, enable a threat-informed defense with breach and attack simulation plus the MITRE ATT&CK framework, and interdict the adversary post-breach to drive down risk.
October 4, 2021
To echo a famous Russian proverb, “trust but verify,” it’s not enough to implement a zero trust architecture. Continuous testing is the only way to achieve real cybersecurity readiness.
September 22, 2021
A landmark innovation from MITRE Engenuity’s Center for Threat-Informed Defense maps cloud security controls in AWS and Azure to MITRE ATT&CK®, elevating cybersecurity effectiveness.
July 16, 2021
The purple team construct is changing cybersecurity for the better. Here is how you build, lead, and manage effective purple team operations.
April 26, 2021
The goal is greater visibility and effectiveness.
April 9, 2021
In advance of the new Biden administration cybersecurity executive order, it’s time for the federal government to get proactive about cybersecurity. Deploying a validated zero trust architecture for the U.S. government’s most critical high-value assets is an aggressive but achievable goal.
February 23, 2021
After SolarWinds, organizations need visibility into their security program effectiveness against real world threats. Automated adversary emulations can help meet that need. By generating real data about how your security program performs against menuPass, you can see security failures, make data-informed adjustments, and plan smart investments to optimize your security. Check out the new emulation plan from MITRE Engenuity’s Center for Threat-Informed Defense and AttackIQ.
October 5, 2020
Last week, the U.S. government’s Cybersecurity and Infrastructure Security Agency (CISA) issued an alert to critical infrastructure owners and operators across the United States to be vigilant for potential Chinese cyberspace operations given heightened tensions between the two countries. What does the CISA alert recommend, and why is it important to follow it?
September 23, 2020
Cybersecurity does not exist in a vacuum and current socio-economic pressures make the United States more vulnerable to cyberattacks of all kinds. With the U.S. presidential election underway, Americans need to take practical steps to defend our democratic processes, online and off. This essay outlines some of the issues facing the United States in advance of the election, shares insights from AttackIQ’s recent podcast with leaders of Harvard’s Defending Digital Democracy project, and offers specific steps to manage the cybersecurity challenges of this moment.