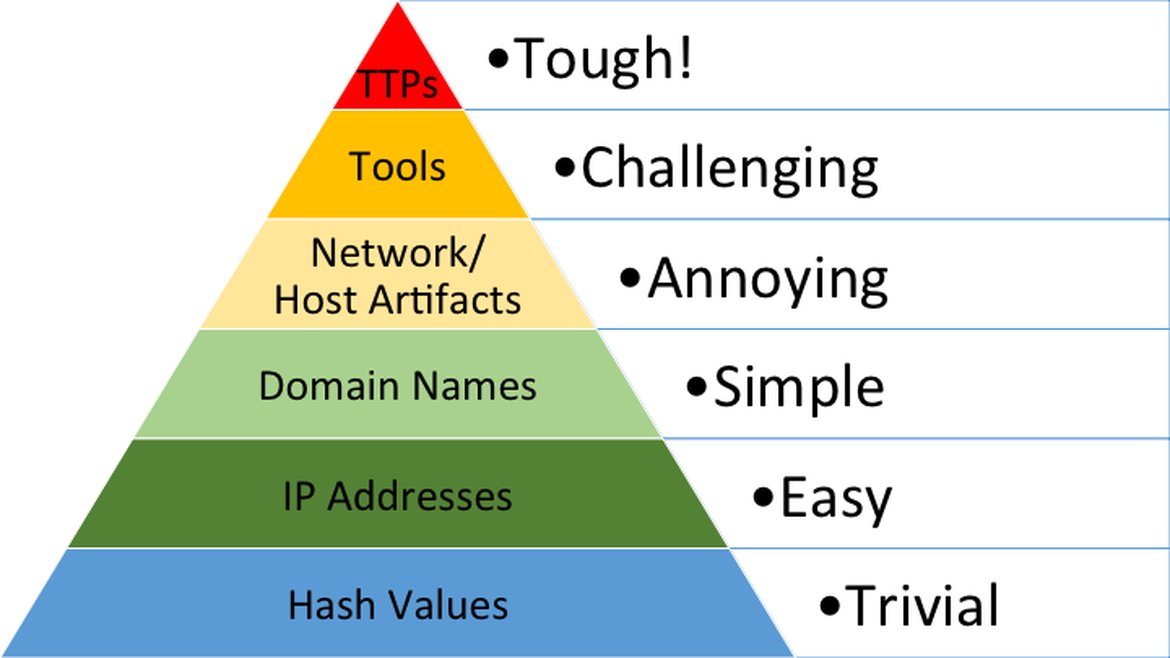
Some of you might be familiar with “The Pyramid of Pain”, first introduced in 2013 by security professional David J Bianco when he was focused on incident response and threat hunting for the purpose of improving the applicability of attack indicators.
Attack Indicators
As you can see in the above diagram, each level of the pyramid represents different types of attack indicators you might use to detect an adversary’s activities and is broken up by how much pain it will cause them when you are able to deny those indicators to them.
As an example, If an adversary is using malware to infect an endpoint within their attack chain and as a defender you are using file hash values to detect such behavior, it is trivial for them to recompile the malware sample such that the file hash value you are using to detect the original sample, is rendered useless. Attackers can and do routinely use polymorphic or metamorphic engines to easily recompute these samples in real-time as they are downloaded to the compromised machines. On the other hand, if your network security controls use IP address, CIDR block or even ASN range blacklists to detect malicious network communication an attacker could move their command and control infrastructure or operations center to another network server, rendering the IP address range you were blocking no longer valuable.
Almost all the levels of indicators have an ephimal value that decays over time. Thus, the importance of maturing your security program to incorporate Threat intelligence to provide an ongoing feed of micro-threat intelligence which will include relevant attack indicators.
One level of the pyramid that has more value than any other level is Attacker TTPs. If a defender can detect or prevent attacker behavior (e.g. MITRE ATT&CK) vs basic artifacts like file hashes or IP addresses, then they make it more costly and more painful for an attacker to pivot their path. To detect and prevent attacker behavior a defender must have security capabilities that use heuristical algorithms which are tougher to build for detection and/or prevention but provide the most resilient security stack.
You can review David’s blog further to go over how each indicator is helpful specifically for incident response and threat hunting, but in this blog, I’m going to briefly review how each level of the pyramid can be used to emulate attacker indicators and validate your security controls.
Emulating Indicators of Attack
| Indicator of Attack | How to Emulate Attacker Activities and Validate Security Controls |
| Hash Values | -Retrieve malware sample based on file hash value
-Pass malware sample through network from one endpoint to another endpoint -Use integrations into security stack to measure prevention and detection technologies for gaps and evidence of true positives |
| IP Addresses | -Emulate connection to destination host IP address e.g. 6.6.6.6
-Use analytics from emulation and integrations into security stack to measure prevention and detection technologies for gaps and evidence of true positives or error that IP address is not accessible |
| Domain Names | -Emulate connection to destination network host domain name e.g. badguy.com
-Use analytics from emulation and integrations into security stack to measure prevention and detection technologies for gaps and evidence of true positives or error that IP address is not accessible |
| Network Artifacts | -Emulate Observables related to the content of various traffic protocols including exact C&C protocol to destination network resource including URI patterns, C2 information embedded in network protocols, distinctive HTTP User-Agent or SMTP Mailer values, etc.
-Use analytics from emulation and integrations into security stack to measure prevention and detection technologies for gaps and evidence of true positives or error that destination network resource is down |
| Host Artifacts | -Emulate specific observables on one or more endpoint/host devices including changes to registry keys or values known to be created by specific pieces of malware, files or directories dropped in certain places or using certain names, names or descriptions or malicious services or almost anything else that’s distinctive
-Use analytics from emulation and integrations into security stack to measure prevention and detection technologies for gaps or evidence of true positives |
| Tools | -Emulate software adversary uses to accomplish their mission e.g Tor, Windows Task Scheduler, GCC, Powershell, etc. The software itself might not be directly malicious, but the specific use, time or location might be indicative of malicious or at least suspicious
-Use analytics from emulation and integrations into security stack to measure prevention and detection technologies for gaps or evidence of true positives |
| Tactics, Techniques and Procedures (TTPs) | -Emulate single or multi-phase attack tactics, techniques and procedures that replicate a pattern of behavior e.g. “Spearphishing with a trojaned PDF file” or “… with a link to a malicious .SCR file disguised as a ZIP” or “Dumping cached authentication credentials and reusing them in Pass-the-Hash attacks”
-Use analytics from emulation and integrations into security stack to measure prevention and detection technologies for gaps or evidence of true positives that artifacts have been detected for each phase of the attack chain |
Conclusion
Within “The Pyramid of Pain”, each level is an opportunity to detect and prevent various indicators of attack. Hash values, IP addresses, and domains are extremely accessible via micro threat intelligence feeds like AT&T ALIEN LABS OPEN THREAT EXCHANGE (OTX) or commercial threat intelligence feeds. It is also possible to find network and host artifacts as observables within micro threat intelligence feeds, but the most resilient security programs will incorporate the ability to detect and prevent attacker tactics, techniques (TTPs) and procedures which describe and help predict future attacker behavior. Attacker TTPS can be consumed through strategic threat intelligence reports, feeds e.g. STIX/STIX2 and frameworks like MITRE ATT&CK. Once you have detection and prevention capabilities in place for each level of “The Pyramid of Pain”, it is critical to validate your security capabilities by emulating attacker activities at each level and proving true security efficacy.
For more information on emulating attacker activity and validating your security controls, email [email protected]